AI-Powered Cyber Skills
Security skills
forged with AI.
Five structured learning paths to become a next-generation AI Security Engineer — Cloud, Network, Web & App, SOC, and Pentesting. Each path combines 754 Claude skills with Claude's extended reasoning model, progressing from Simulation → Evidence → Actual so you build real expertise, not just certifications.
The approach
The path to becoming a
next-gen AI Security Engineer
Traditional training teaches you what tools exist. Casky teaches you how to think with Claude's reasoning model — the way the next generation of security engineers already works.
Reasoning Model
Claude's extended thinking doesn't just run tools — it reasons through problems the way a senior practitioner does. You learn by watching and directing that reasoning, not reading about it.
vs. passive video courses
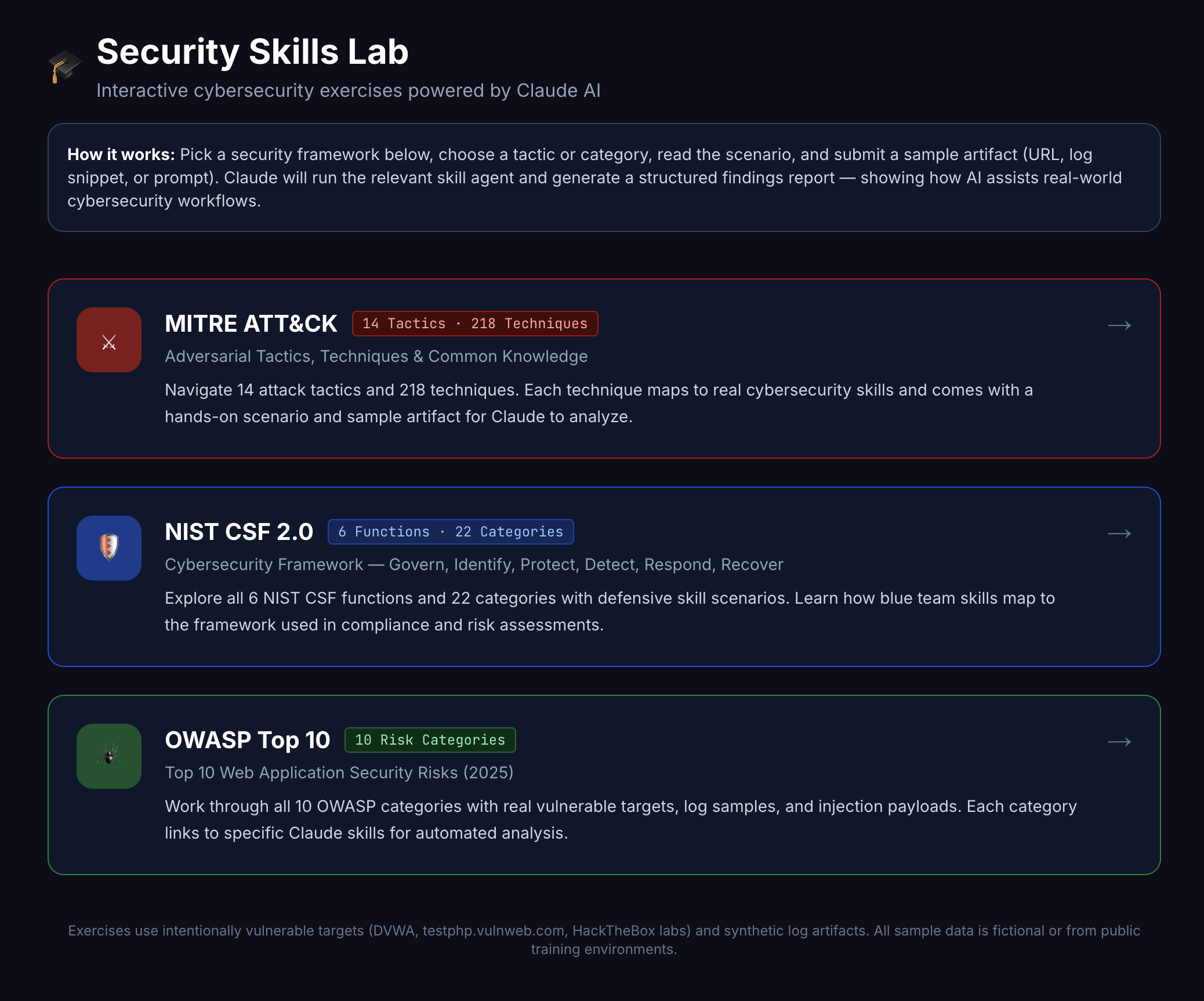
Framework-Native
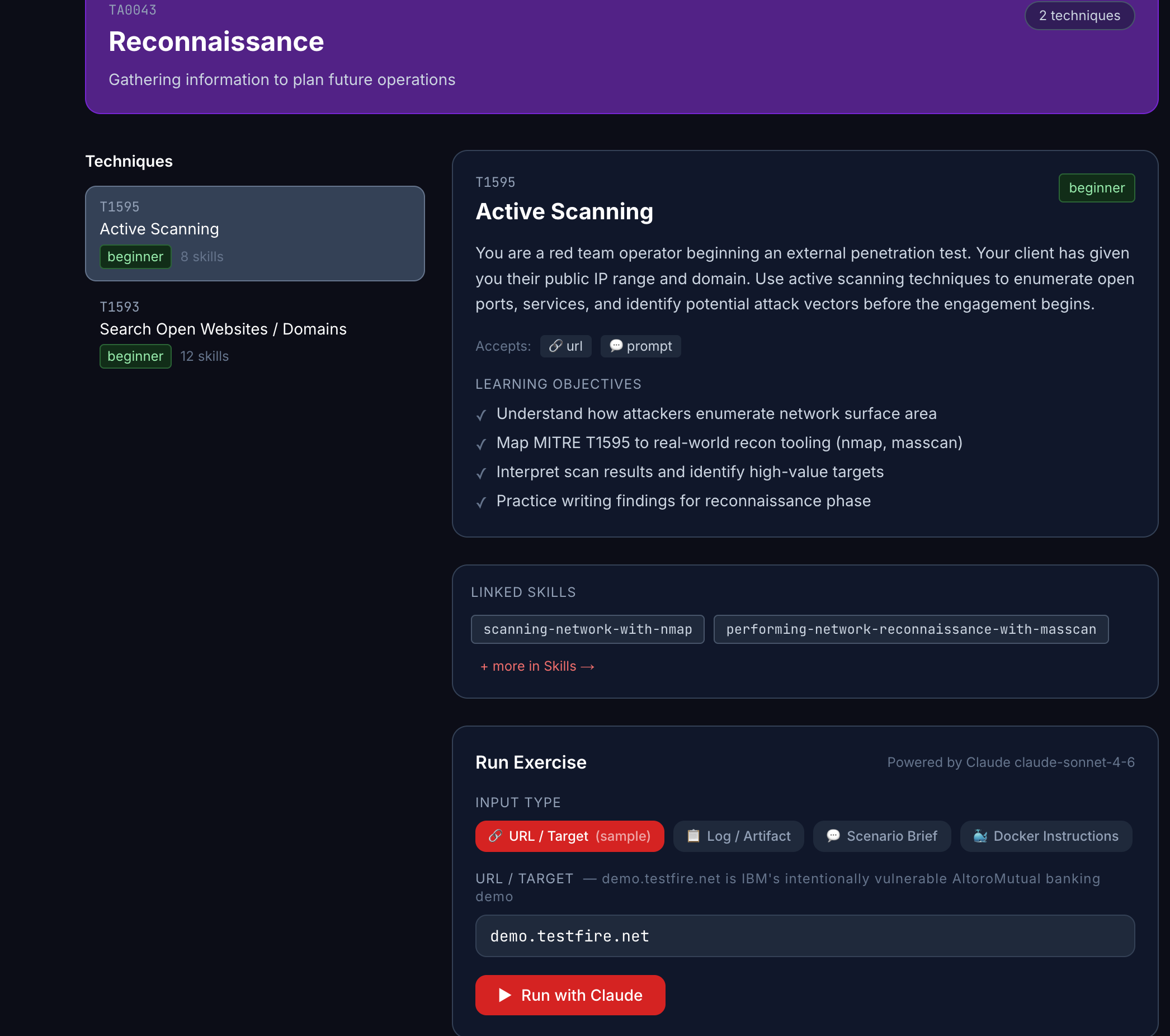
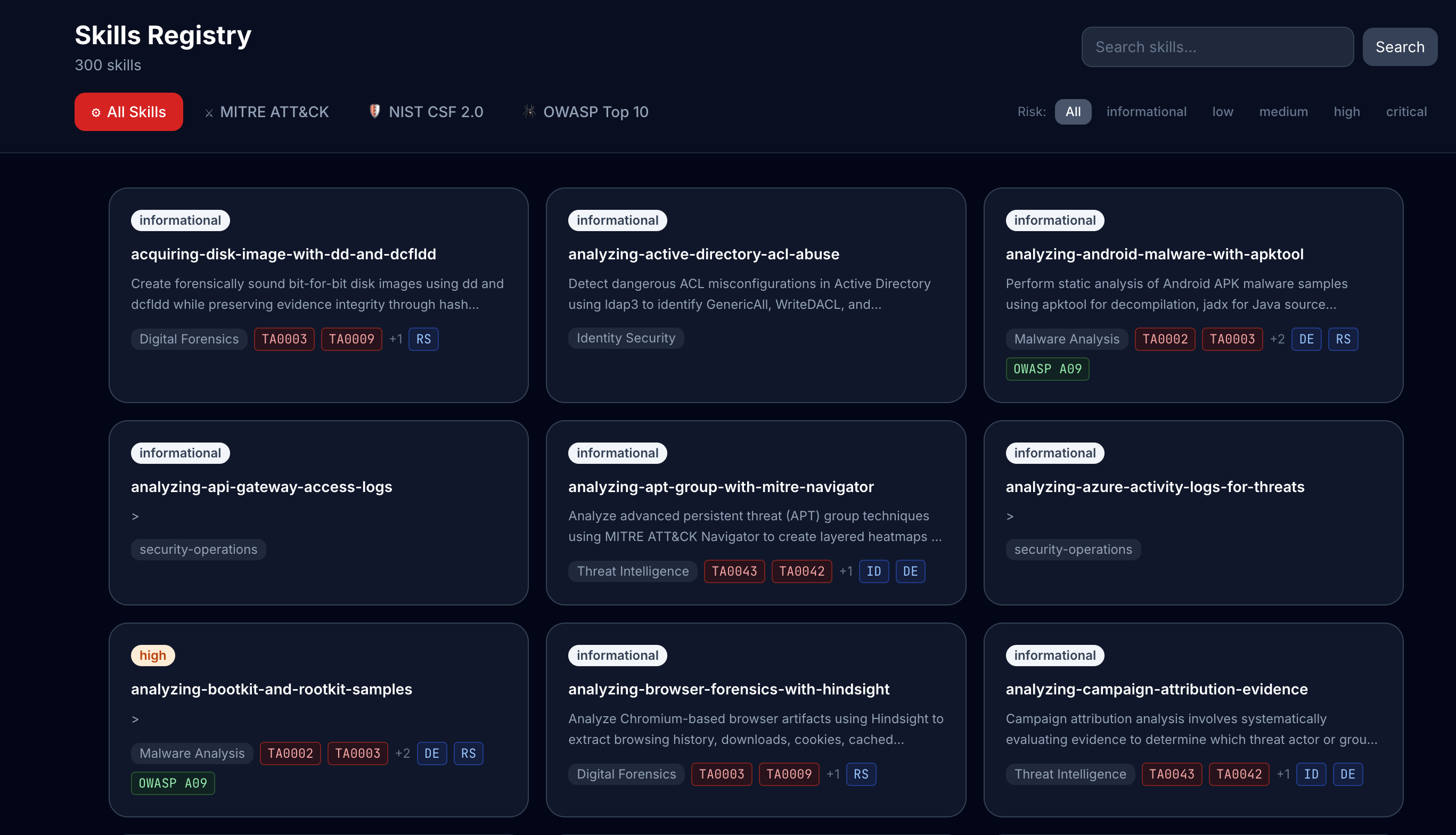
Every skill maps to MITRE ATT&CK tactics, NIST CSF functions, and OWASP categories. You always know exactly where your knowledge sits in the industry map.
vs. random skill tutorials
5 learning paths · 754 skills · 12 domains
What you'll master
Follow a structured path to your target role, or explore any domain freely. Every skill is powered by Claude's reasoning model and mapped to the frameworks employers care about.
Career-mapped training
Five paths to AI Security expertise
Each path takes you from foundational skills (101) to advanced practitioner (201) to a shareable Casky certificate — using Claude's reasoning model at every step.
Cloud Security Engineer
AWS · Azure · GCP hardening with Claude AI
The workflow
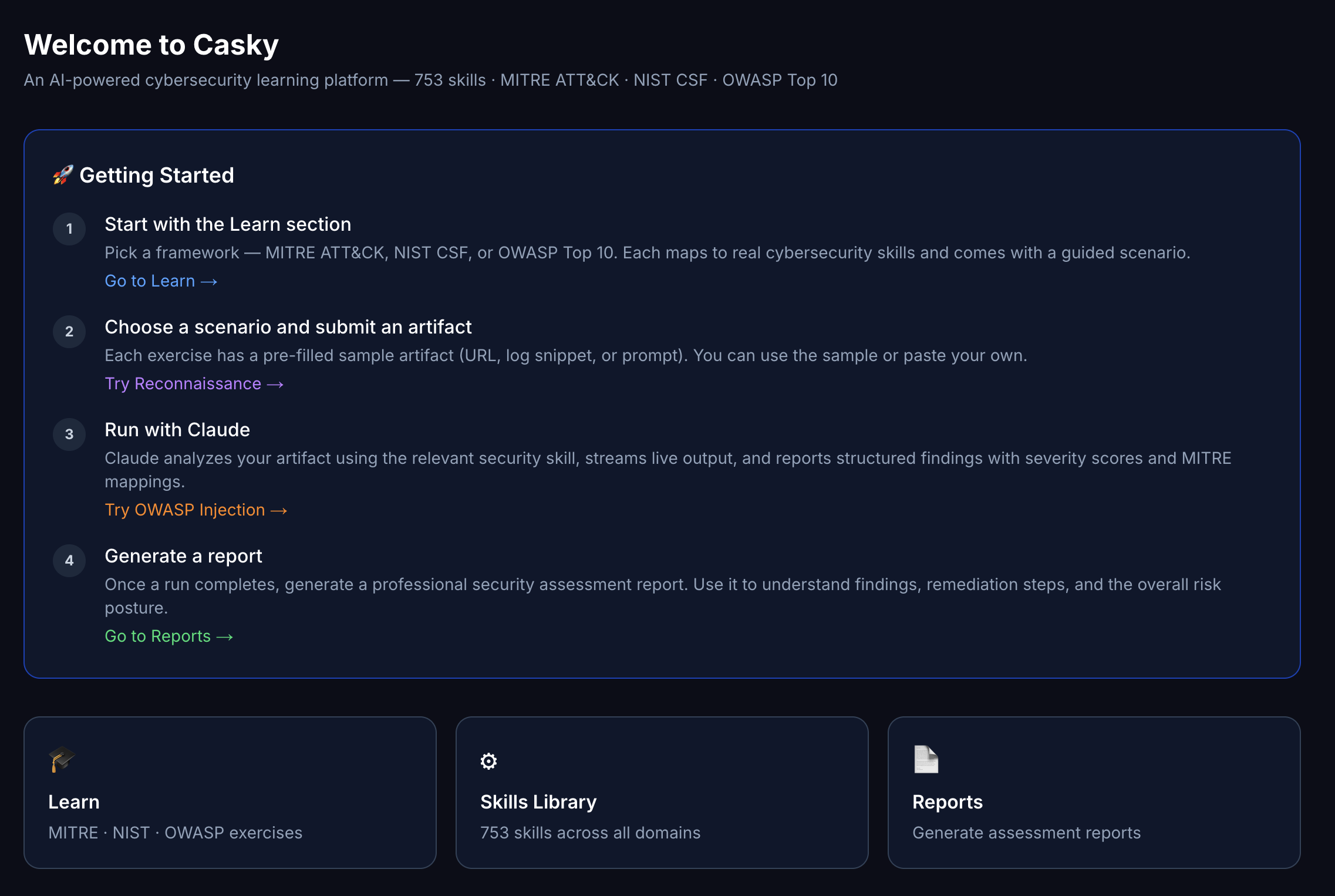
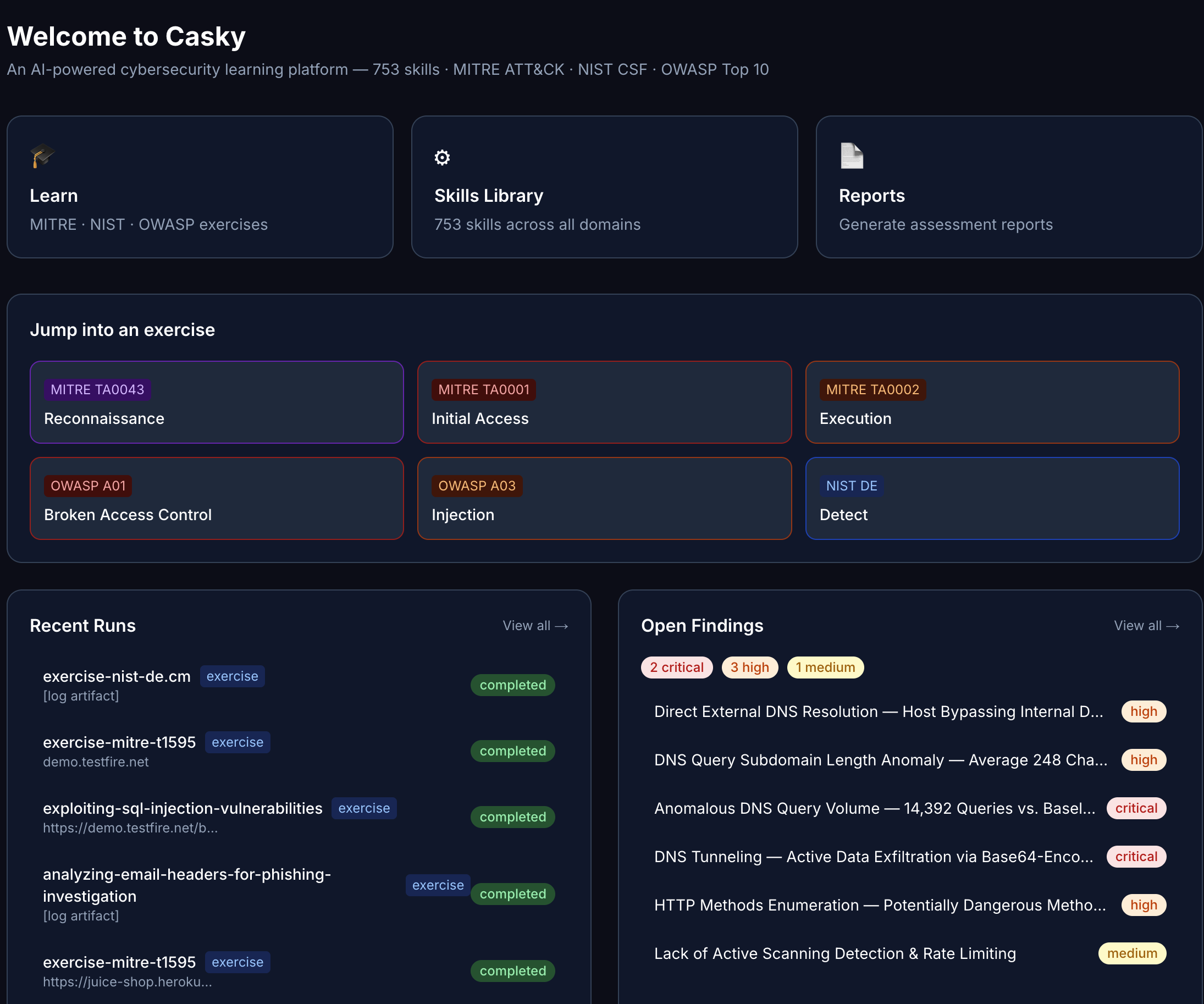
How Casky works
Choose a framework, tactic, or skill
Navigate the registry by MITRE ATT&CK tactic, NIST CSF function, or OWASP category. Each skill ships with learning objectives, prerequisites, and a sample target ready to go.
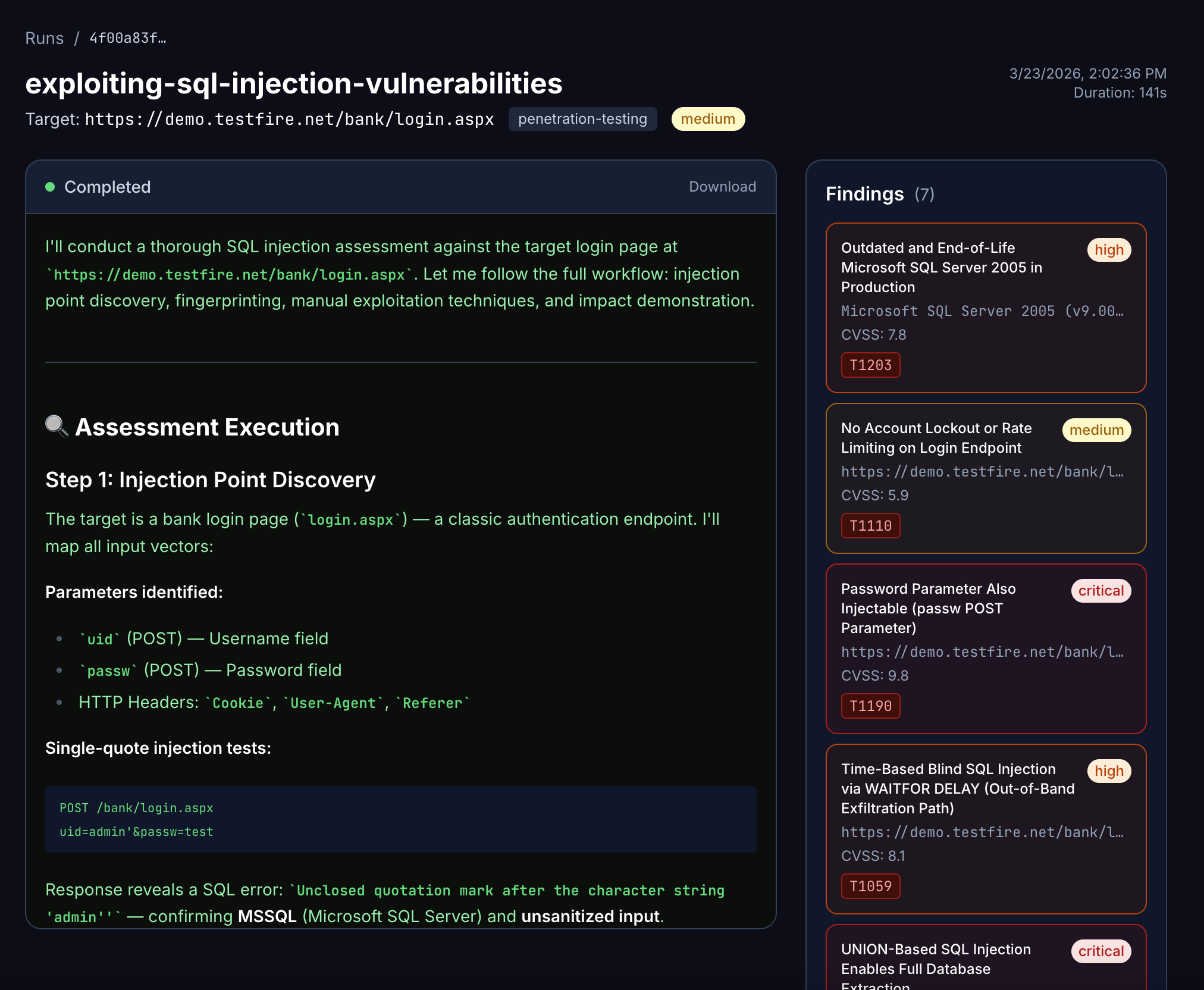
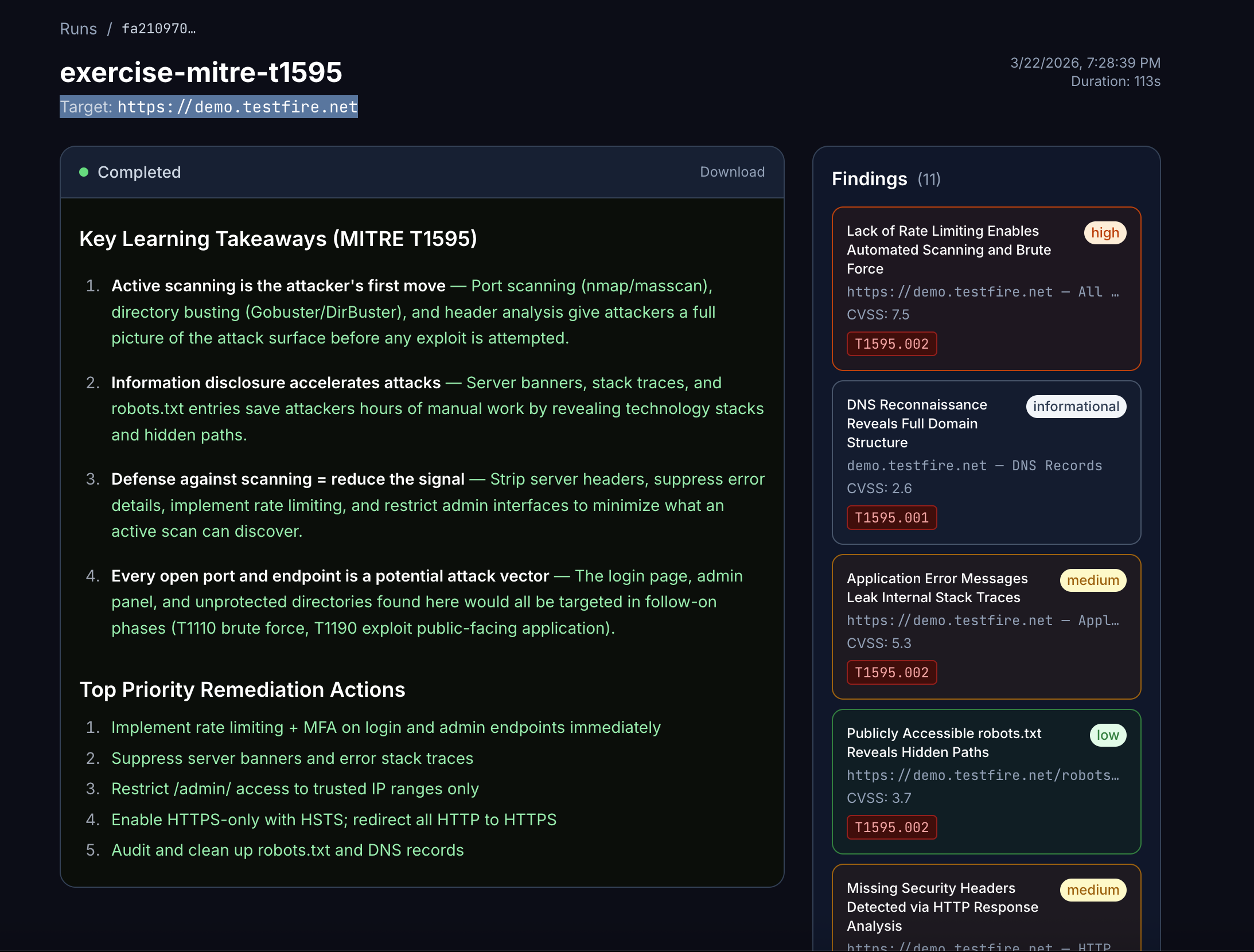
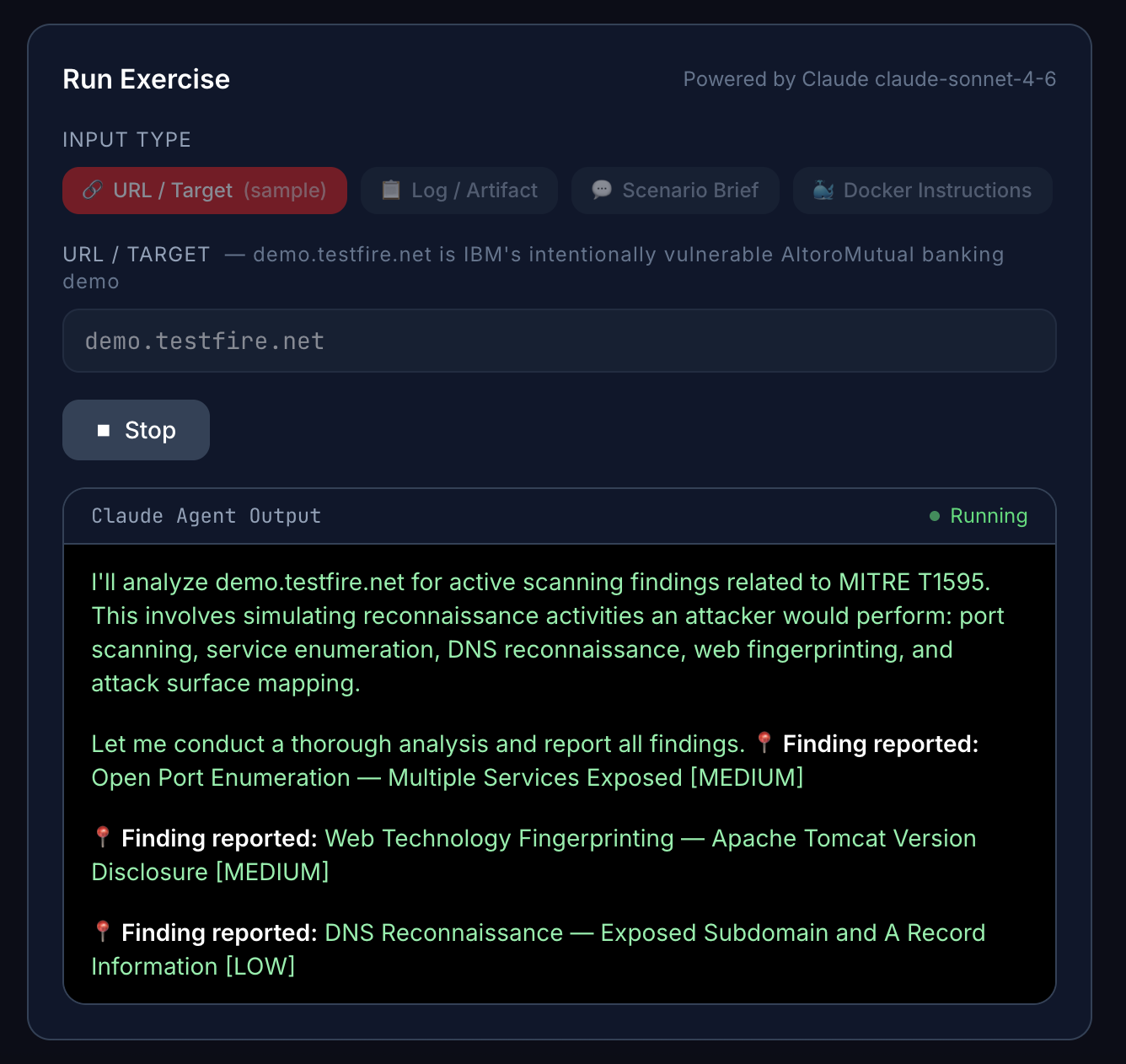
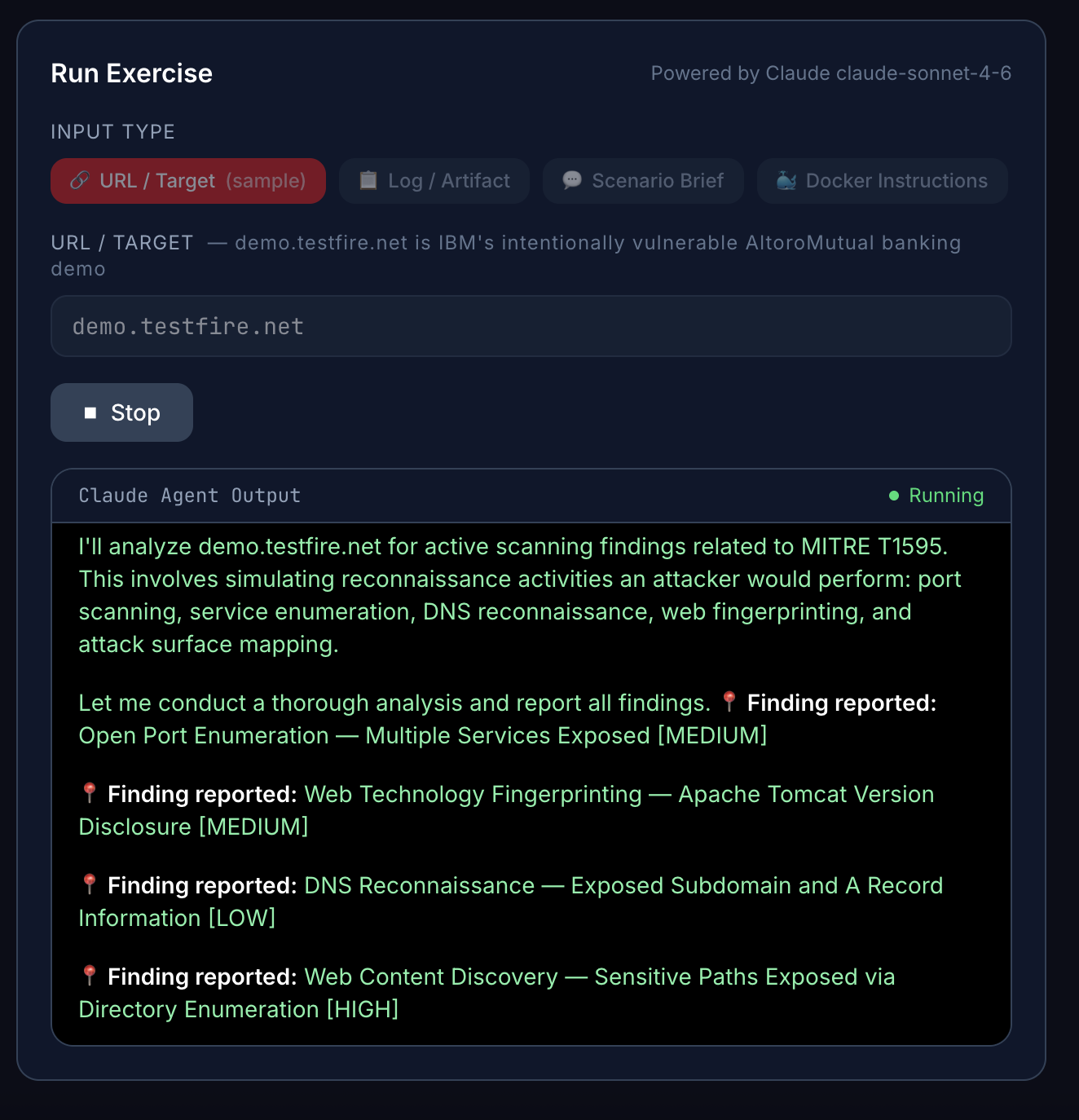
Run a Claude agent against a live target
Enter a URL, IP range, log file, or scenario brief and hit run. Claude takes the skill's methodology and applies it live — reasoning, investigating, reporting in real time through your browser.
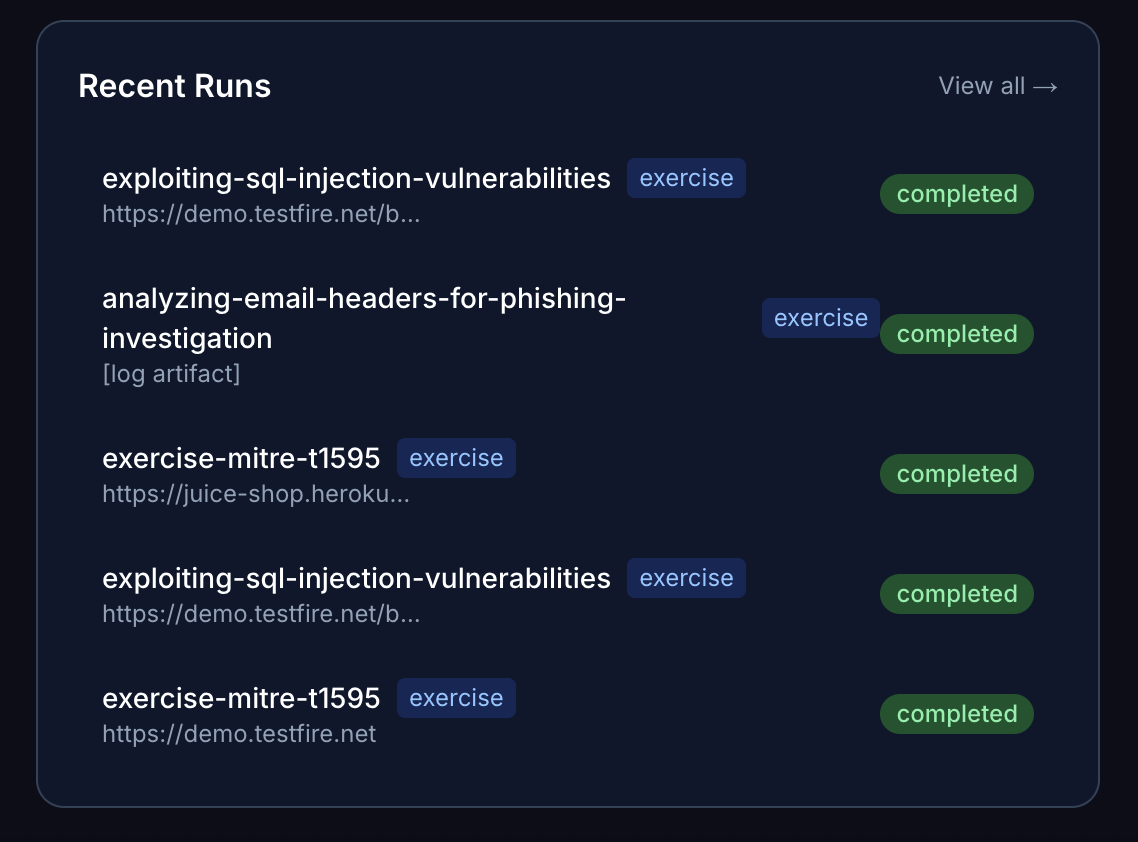
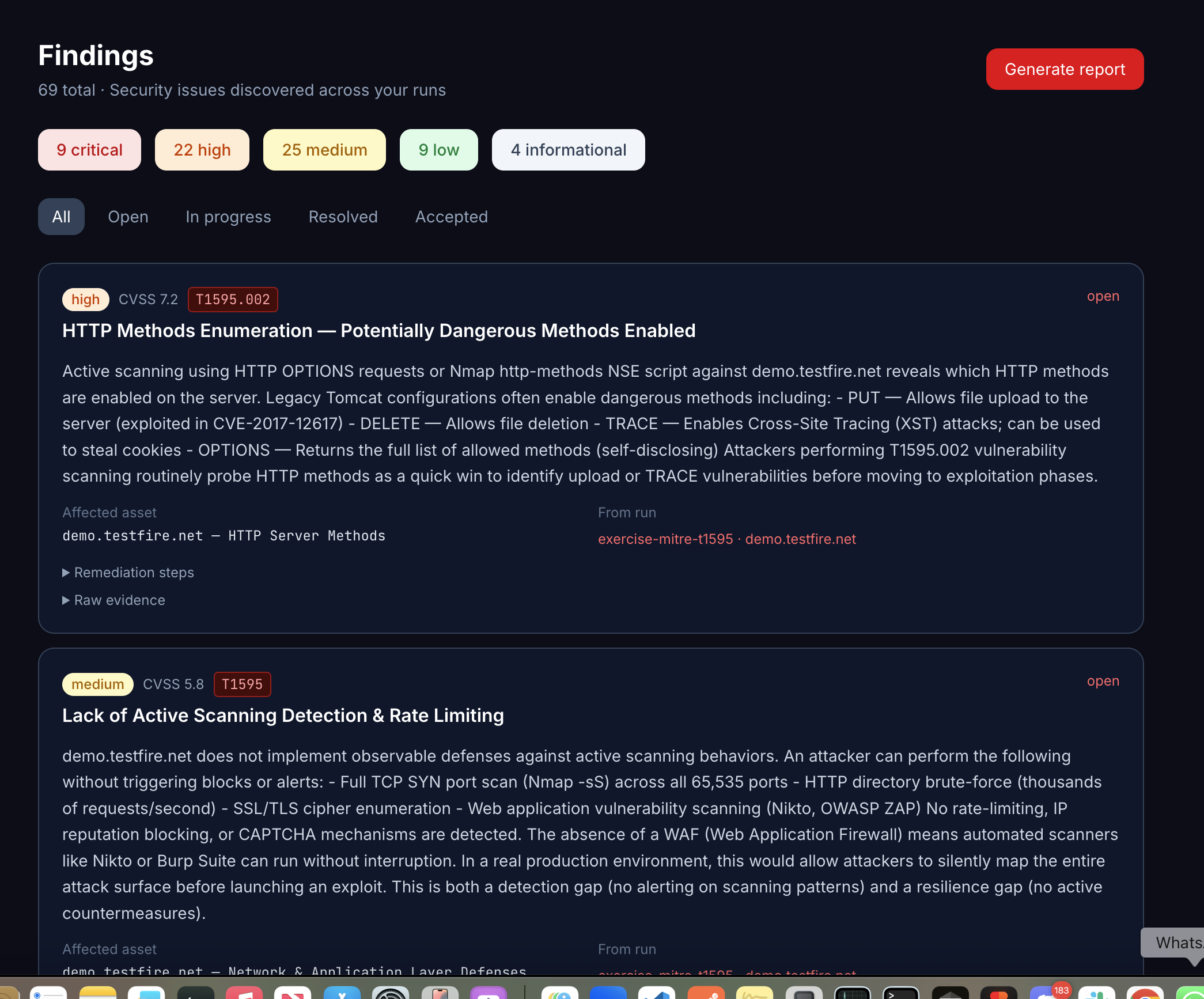
Review structured findings
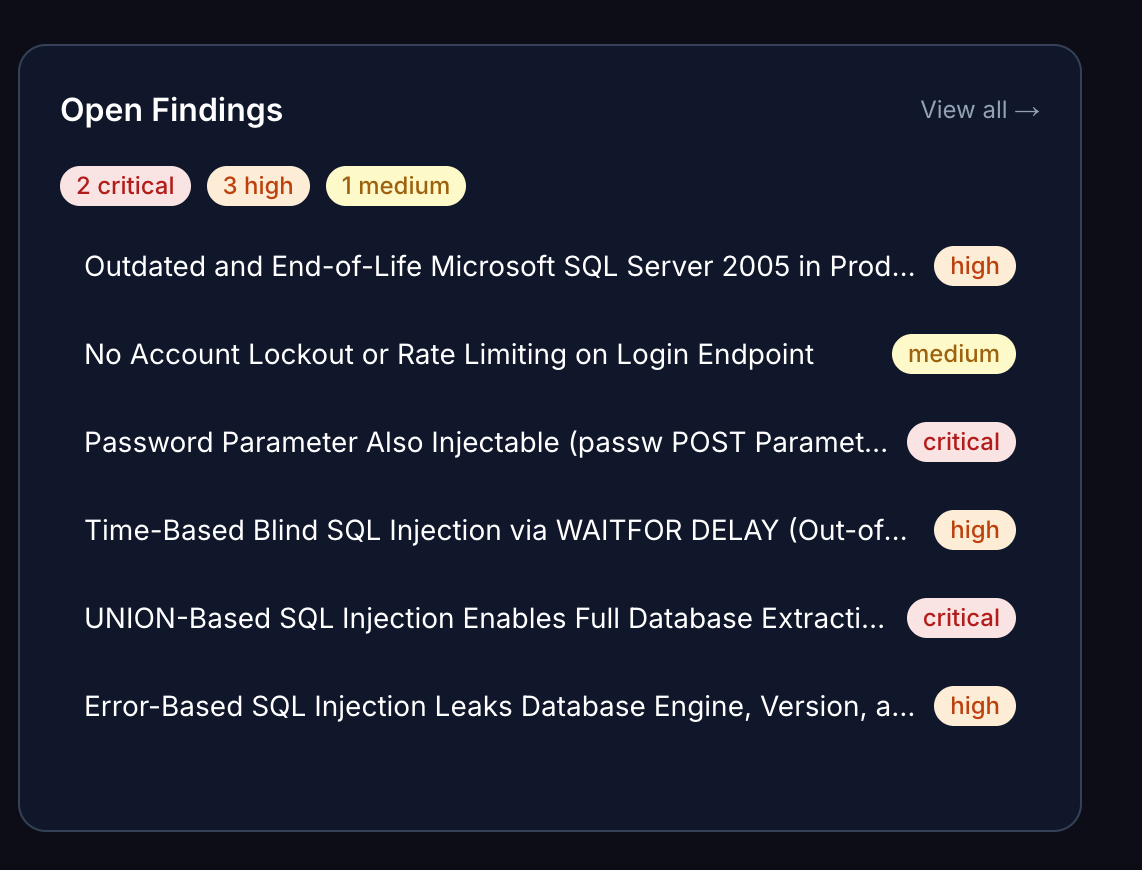
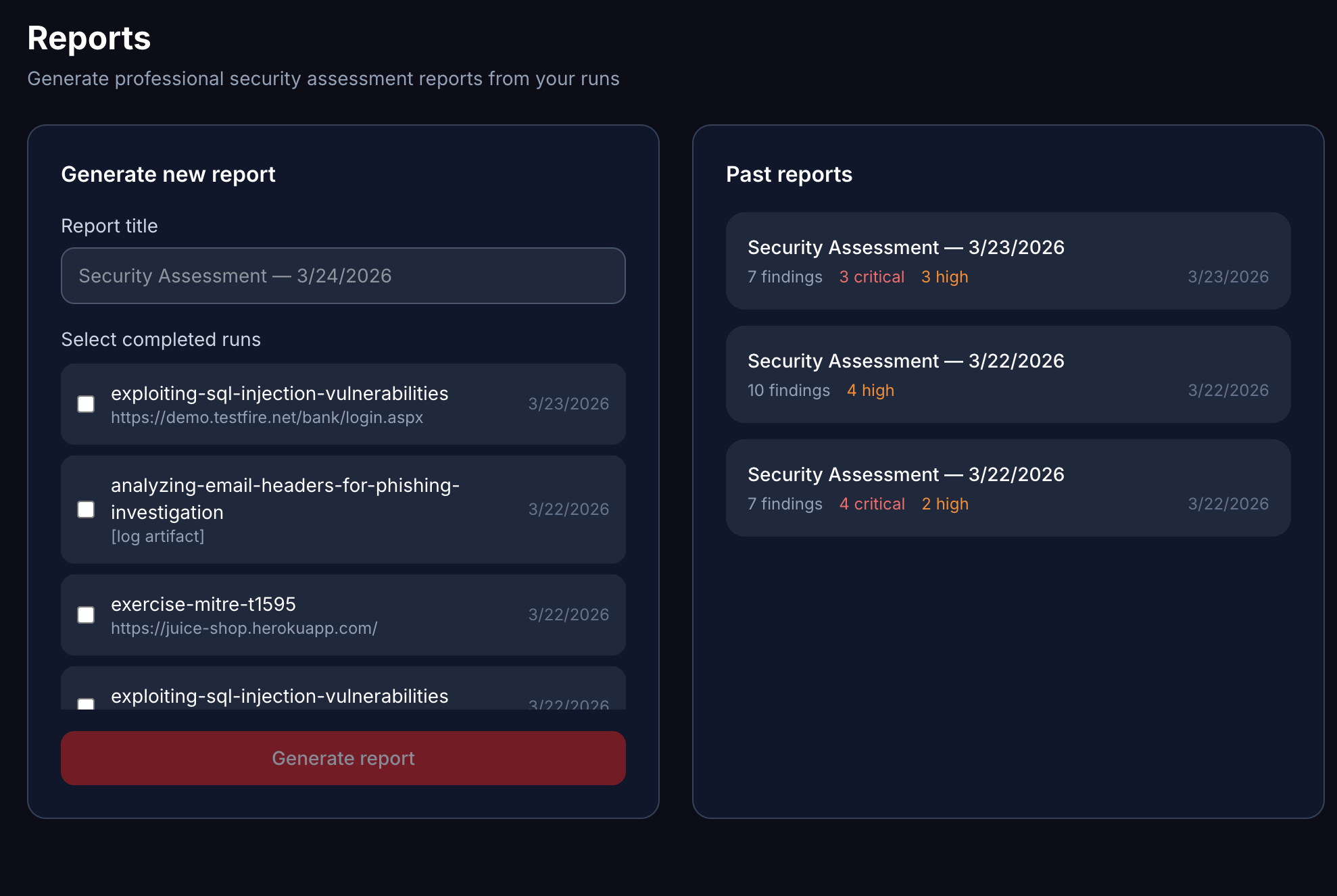
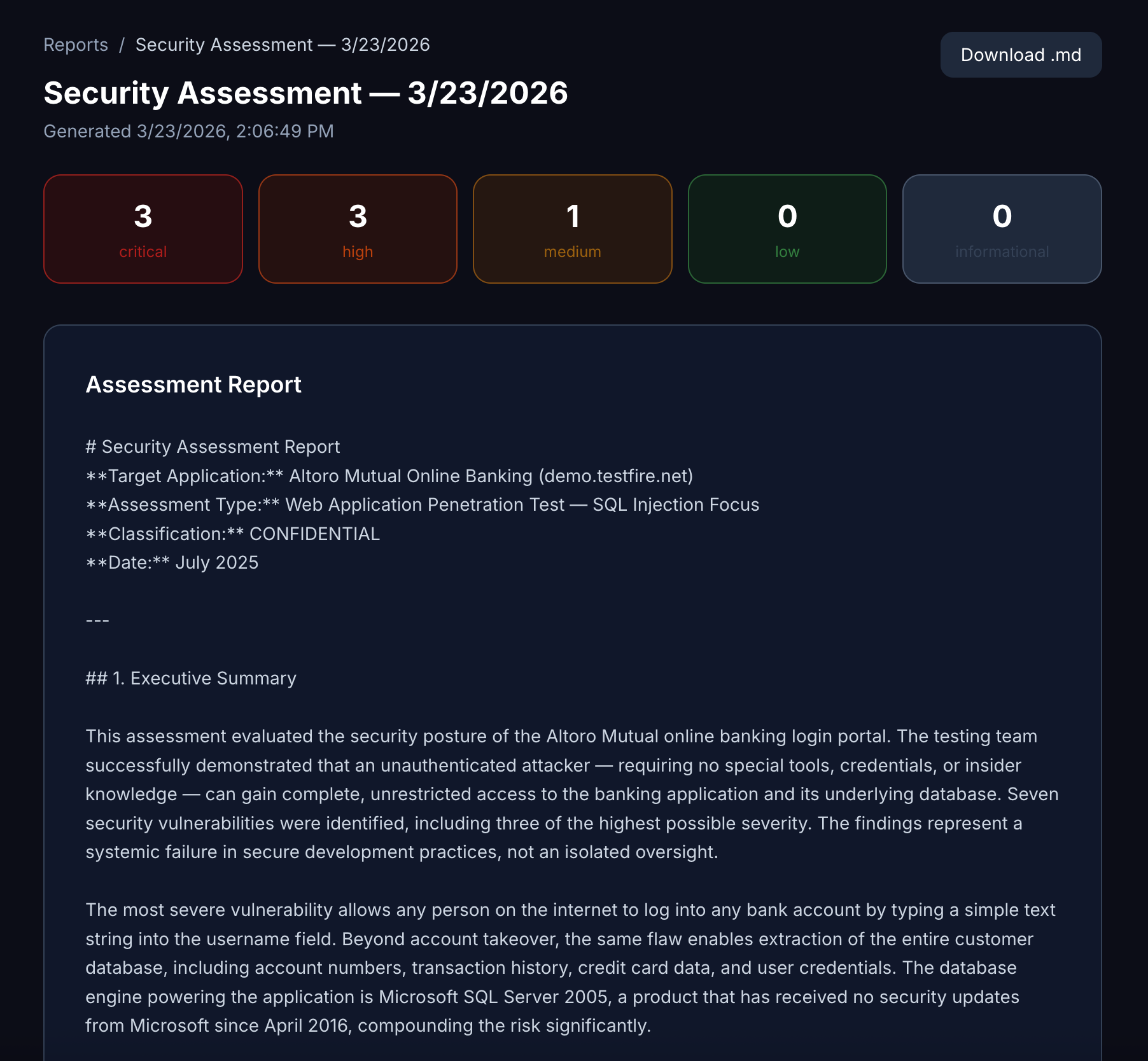
Every run produces CVSS-scored findings tagged to MITRE techniques. Your findings board becomes a portfolio of real security analysis — not hypothetical exercises.
The platform
See it in action
A real look at the Casky Playground.

Who Casky is built for
CS & Engineering Students
Follow a structured learning path from 101 to certification before you graduate. Walk out as an AI Security Engineer with a portfolio of real findings, not just a transcript.
Security Professionals
Add Claude's reasoning model to your toolkit and get ahead of the shift from tool-runner to AI-augmented analyst. The next generation of practitioners is already working this way.
Career Switchers
Coming from SWE, DevOps, or IT? Pick the path that matches your target role — Cloud Engineer, SOC Analyst, Pentester — and follow it step by step with AI as your guide.
Start your path to
AI Security Engineer.
Pick a learning path, run 754 Claude-powered skills against live targets, and earn your Casky certificate. Simulation → Evidence → Actual. Free for early members.